Amazon’s AWS WAF web application firewall service is built specifically to protect cloud apps from a whole range of Internet threats. Learn how it works.
We all know that web applications are vulnerable to attacks, and that deploying your application from the cloud can theoretically expose it to even greater risk. To help secure their web apps, administrators will often use IDS (Intrusion Detection System) or IPS (Intrusion Prevention System) solutions, or a Web Application Firewall. In this post we’re going to focus on WAFs and, in particular, Amazon’s AWS WAF application-level firewall service.
Because it monitors traffic at the application layer, WAF will often be the preferred choice for securing your applications. Let’s see how it works, and how Amazon’s version can take it even further.
Categories of web attacks
Before talking about AWS WAF, it makes sense to review some of the more common vulnerabilities facing web applications.
- DDoS attacks
This is probably the most common attack of them all. Attackers overload an application by sending bulk requests to the web servers. This slows down the application and makes it unavailable for genuine requests. This can significantly hurt the value of a brand and also affect business.
- SQL injections
An attacker can run malicious SQL queries on websites or applications using SQL based databases. If the databases aren’t secured, attackers can access confidential account and business information.
Here’s an example of SQL injection:
SELECT id FROM users WHERE username=’username’ AND password=’password’ OR 1=1’
The above statement – even using an incorrect username or password – will always return a result.
- Cross site scripting
If your application is vulnerable to cross site scripting then the attacker can run or inject malicious scripts, generally in the form of a browser side script. If your end user is accessing a vulnerable application, his browser has no way to know that the script should not be trusted, and will execute it. These scripts can even rewrite the content of the HTML page.
These threats should certainly give us some worry. But hey, all is not lost. The web application firewall is there to help. There are many WAF tools available on the market like ModSecurity, WebCastellum, OpenWAF, and Barracuda. But now there’s also AWS WAF.
What is AWS WAF?
Now, as we all know, AWS is riding on top of the cloud computing wave. Customers are migrating all kinds of applications to AWS’s infrastructure. But the basic challenges of security remain the same: how can you protect your web applications from all the vulnerabilities we’ve discussed (along with those we didn’t mention)? Can I use the traditional WAF tools with the cloud? Will they work with my AWS infrastructure?
Yes and yes. But let’s take it one step at a time. Let’s consider a simple use case. Imagine that you have an application with some web servers, app servers, and a database, all deployed in the AWS cloud. You’d obviously like to secure your application from web attacks. How should you proceed?
The traditional approach would be to set up a firewall in front of your web servers to monitor application traffic before it hits the servers. If you’re using AWS, then most probably, it would sit between Amazon’s load balancer and the servers. You could also place it in front of the load balancer.
Watch this short video which is part of the Cloud Academy’s Protecting Web Apps with AWS WAF, Shield & Firewall Manager Course.
Design considerations
- Choosing an appropriate WAF solution and managing its availability can really drive you crazy.
- Setup and configuration can be very complex.
- Making sure your WAF solution can keep up with your application as it scales can be a challenge.
- Web traffic monitoring may not be simple.
To address these issues, Amazon has given us AWS WAF, this will protect AWS-powered web applications served by AWS services like Amazon CloudFront from attacks happening at application layer.
AWS WAF is a web application firewall that helps protect your web applications from common web exploits that could affect application availability, compromise security, or consume excessive resources. AWS WAF gives you control over which traffic to allow or block to your web application by defining customizable web security rules.
How AWS WAF works
Now, instead of provisioning and maintaining your own WAF servers, you can just set up WAF from the AWS console. This will let you define your traffic filtering rules without needing to invest time ensuring proper configuration and availability.
To get started, you only need to create web ACLs. A web ACL contains at least one rule in which you specify conditions that will either block or allow incoming requests. Assuming you’re working with CloudFront, once the web ACL is ready, you can simply attach it to your application’s distribution. It’s important to understand a few key web ACL elements, like Conditions and Rules:
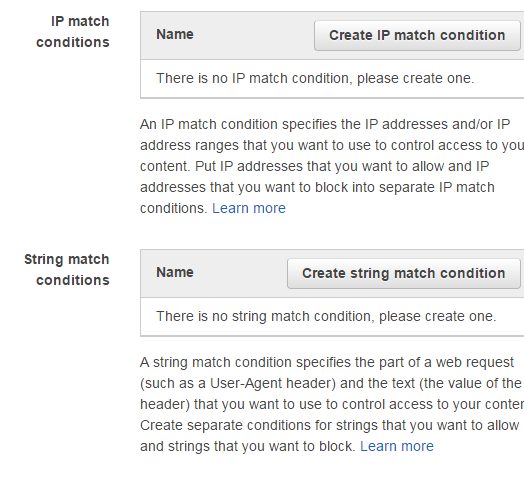
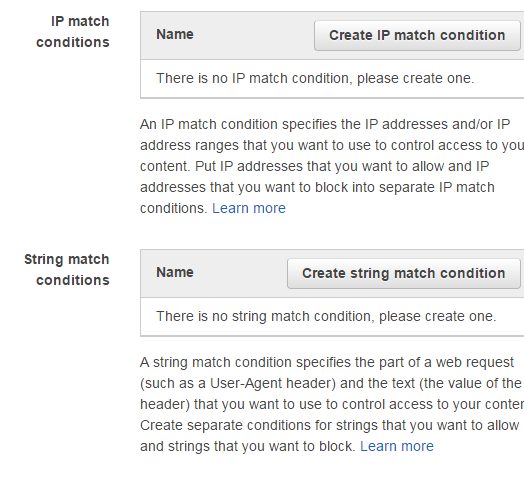
WAF Conditions
For your rules to work, you will need to specify the filter condition for your web ACL:


WAF Rules
Once you are done with configuring conditions, you can create a rule and attach it to your web ACL. You can attach more than one rule to an ACL.






You’re now ready to associate your new web ACL with an AWS service.
Pricing
With AWS WAF, you pay only for what you use. There are no minimum fees and no upfront commitments. Your costs will depend on three major variables:
- Number of Web ACLs: each Web ACL will cost you $5/month.
- Number of Rules: $1.00 per rule per web ACL per month.
- Request Count: $0.60 per million web requests.
Things to know about AWS WAF
- Since AWS WAF is integrated with AWS CloudFront – which supports custom origins outside of AWS – it can even be used to protect websites not hosted on AWS.
- You can configure custom error pages.
- Real time metrics can be monitored from CloudWatch.
- AWS WAF can inspect HTTPS traffic.
I hope this post helped give you a clear picture of AWS’s Web application firewall and its implementation.
If you’ve got any thoughts of your own, why not add them to the comments?



