AWS CloudFormation lets you create and provision AWS infrastructure deployments predictably and repeatedly using templates.
Cloud deployment, and specifically AWS cloud deployment, can be a daunting task and AWS provides many us with many useful tools. However, this time I am going to focus on my personal favorite cloud deployment option: CloudFormation.
Once you’ve launched a few CloudFormation installations, you can use these templates over again and again, which is extremely helpful if you need to constantly deploy new infrastructure. Best of all AWS has pre-built templates that you can use or modify to your heart’s content.
AWS CloudFormation Best Practices
As with all AWS services, before you start it’s a good idea to do some research. Of course, there AWS’s own documentation, but I’ll offer you a brief CloudFormation best-practice summary:
Planning and organizing
- Organize your stacks by Lifecycle and Ownership (use the lifecycle and ownership of your AWS resources to help you decide what resources belong in each stack).
- Reuse Templates to replicate stacks in multiple environments (to make templates reusable, use the parameters, mappings, and conditions sections so that you can customize your stacks when you create them).
- Verify quotas for all resource types (before launching a stack, ensure that you can create all the resources that you want without hitting your AWS account limits).
- Use Nested Stacks to reuse common Template patterns (separate out common components and create dedicated templates for them).
Creating templates
- Do not embed credentials in your Templates (use input parameters to pass in information whenever you create or update a stack).
- Use AWS-Specific Parameter Types (you can specify a parameter as type
AWS::EC2::KeyPair::KeyName). - Use Parameter Constraints (describe allowed input values so that AWS CloudFormation catches any invalid values before creating a stack).
- Use AWS::CloudFormation::Init to deploy software applications on Amazon EC2 instances (install and configure software applications on Amazon EC2 instances by using the cfn-init helper script and the
AWS::CloudFormation::Initresource). - Validate Templates before using them (validating a template can help you catch syntax and some semantic errors ).
Managing stacks
- Manage all stack resources through AWS CloudFormation (do not make changes to stack resources outside of AWS CloudFormation).
- Use Stack Policies (stack policies help protect critical stack resources from unintentional updates).
- Use AWS CloudTrail to log AWS CloudFormation calls (CloudTrail tracks anyone making AWS CloudFormation API calls in your AWS account).
- Use code reviews and revision controls to manage your templates (to review changes and to keep an accurate history of your resources).
If you are going to create your own templates then it is in your best interests to try and adhere to these best practices, as they’re based on real-world experience from active AWS CloudFormation users.
What does a template look like?
A CloudFormation template is a JSON-formatted text file that describes your AWS infrastructure. Templates include several major sections. Here are the most common sections that you’re likely to find in a CloudFormation template:
Note: the Resources section is the only section that is actually required!
{
"AWSTemplateFormatVersion" : "version date",
"Description" : "JSON string",
"Metadata" : {
//template metadata
},
"Parameters" : {
//set of parameters
},
"Mappings" : {
//set of mappings
},
"Conditions" : {
//set of conditions
},
"Resources" : {
//set of resources
},
"Outputs" : {
//set of outputs
}
}
Launching a template
As stated previously, the good news is that AWS has lots of sample templates available for each region.
Because each region might have different requirements, a template that works in one region might not work in another region.
The following example uses the Asia Pacific (Sydney) Region. Let’s choose a template and prepare to launch it.
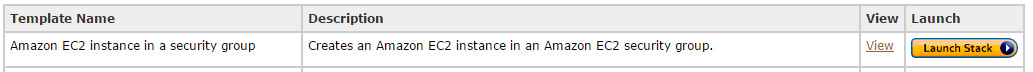
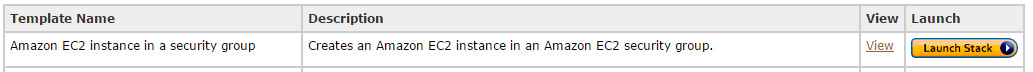
- Choose your template. I am going to use the template “Amazon EC2 instance in a security group” which, as you should be able to guess, creates an Amazon EC2 instance in an Amazon EC2 security group. You can view the template here.
- Click on the “Launch stack” button as shown here:
- On the “Select Template” page just click NEXT as you have already chosen your template.
- You will now come to “Specify Parameters” page. This presents the template’s parameters:
"Parameters" : {
"KeyName": {
"Description" : "Name of an existing EC2 KeyPair to enable SSH access to the instance",
"Type": "AWS::EC2::KeyPair::KeyName",
"ConstraintDescription" : "must be the name of an existing EC2 KeyPair."
},
"InstanceType" : {
"Description" : "WebServer EC2 instance type",
"Type" : "String",
"Default" : "m1.small",
"AllowedValues" : [ "t1.micro", "t2.micro", "t2.small", "t2.medium", "m1.small", "m1.medium", "m1.large", "m1.xlarge", "m2.xlarge", "m2.2xlarge", "m2.4xlarge", "m3.medium", "m3.large", "m3.xlarge", "m3.2xlarge", "c1.medium", "c1.xlarge", "c3.large", "c3.xlarge", "c3.2xlarge", "c3.4xlarge", "c3.8xlarge", "c4.large", "c4.xlarge", "c4.2xlarge", "c4.4xlarge", "c4.8xlarge", "g2.2xlarge", "r3.large", "r3.xlarge", "r3.2xlarge", "r3.4xlarge", "r3.8xlarge", "i2.xlarge", "i2.2xlarge", "i2.4xlarge", "i2.8xlarge", "d2.xlarge", "d2.2xlarge", "d2.4xlarge", "d2.8xlarge", "hi1.4xlarge", "hs1.8xlarge", "cr1.8xlarge", "cc2.8xlarge", "cg1.4xlarge"],
"ConstraintDescription" : "must be a valid EC2 instance type."
},
"SSHLocation" : {
"Description" : "The IP address range that can be used to SSH to the EC2 instances",
"Type": "String",
"MinLength": "9",
"MaxLength": "18",
"Default": "0.0.0.0/0",
"AllowedPattern": "(\\d{1,3})\\.(\\d{1,3})\\.(\\d{1,3})\\.(\\d{1,3})/(\\d{1,2})",
"ConstraintDescription": "must be a valid IP CIDR range of the form x.x.x.x/x."
}
- I am going to choose t1.micro, name my key pair, and leave SSH Location as default. Click NEXT.
- On the options page, I suggest Key=Name and Value={any name you want to describe it}. Click NEXT.
- Review the Page then click CREATE.
- Click CREATE STACK in top left corner
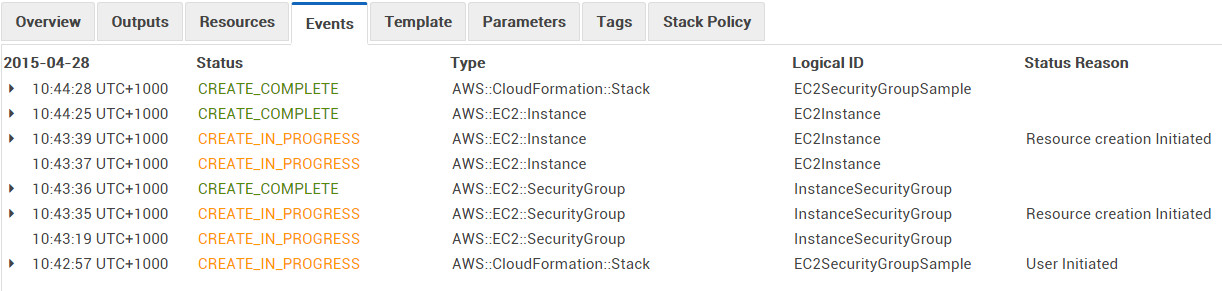
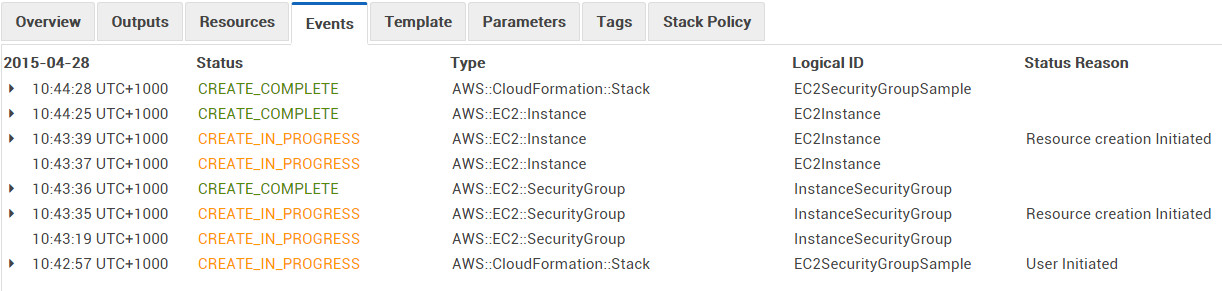
- You should then see CREATE_IN_PROGRESS
- Refresh screen after a minute or two and you should see CREATE_COMPLETE
- Click on the stack name and then on the Events tab. You should see a screen similar to this:
Summary
The above is probably the simplest example of a CloudFormation deployment. Here are some more things you could do on AWS with the simple click of a launch button:
- Create a DynamoDB table with global and local secondary indexes.
- Create an AWS OpsWorks stack with a load-balanced application that runs inside a designated VPC.
- Create an Amazon RDS database instance with provisioned IOPs.
- Create a publicly accessible Amazon S3 bucket that is configured for website access.
Other CloudFormation resources
If you’d like to dig a bit deeper into CloudFormation, try:



