As ever, cloud security is the number-one priority for AWS. During the Tuesday Night Live event, just hours before Andy Jassy’s keynote, AWS announced the launch of Amazon GuardDuty, now the 10th service in the AWS Security, Identity & Compliance category.
What is Amazon GuardDuty?
Amazon GuardDuty is an intelligent threat detection service. It allows users to monitor their AWS account for unusual and unexpected behavior and to analyze and monitor existing logs, such as CloudTrail Event Logs, VPC Flow Logs, and DNS Logs. It assesses data from multiple feeds with a focus on threat detection by looking for anomalies and known malicious sources such as IP addresses and URLs.
The service itself is powered by Machine Learning, which allows it to continuously evolve and understand your infrastructure. Amazon GuardDuty looks at erroneous patterns with your AWS account that could indicate potential threats to your environment. These threats could be behavioral based, where a resource has been compromised by account or credential exposure, unexpected API calls that sit outside security best practices, or even communications from suspicious sources.
Using the threat detection feeds, which can be generated from public sources or provided from within AWS itself, this service provides automatic and continuous security analysis for safeguarding your entire AWS environment.
Getting Started
GuardDuty analyzes a number of your logs within your account. To activate this service, the following service role permissions are automatically generated:
{
“Version”: “2012-10-17”,
“Statement”: [
{
“Effect”: “Allow”,
“Action”: [
“ec2:DescribeInstances”,
“ec2:DescribeImages”
],
“Resource”: “*”
}
]
}
The service can then assume this role using the following Trust Relationship, which is also created during activation:
{
“Version”: “2012-10-17”,
“Statement”: [
{
“Effect”: “Allow”,
“Principal”: {
“Service”: “guardduty.amazonaws.com”
},
“Action”: [
“sts:AssumeRole”
]
}
]
}
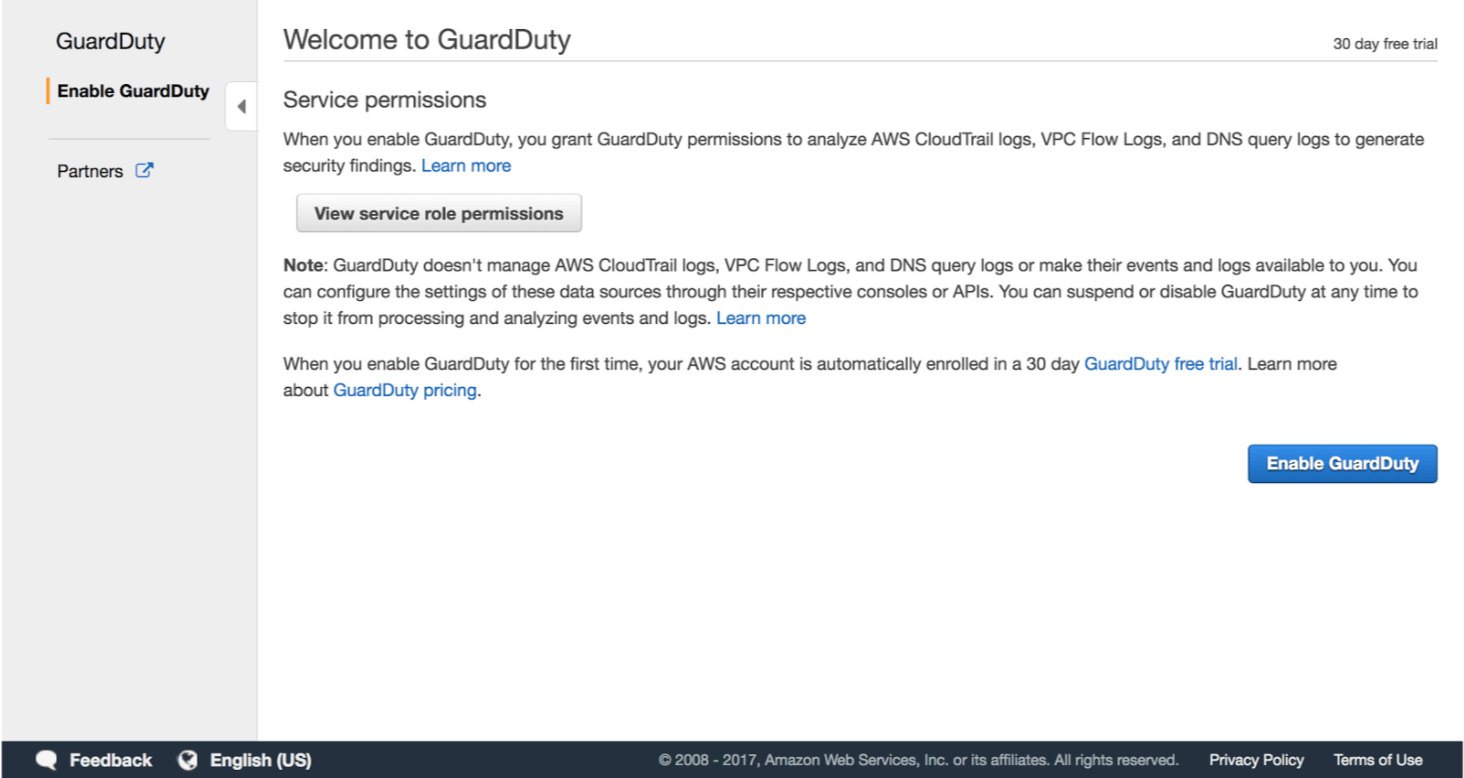
The service itself is very easy to enable within your account. Simply click “Enable GuardDuty” within the service dashboard in the AWS management console:
Once enabled, the service will begin analysis right away. Any findings will be displayed on the dashboard. By categorizing each as low, medium, or high, you can immediately focus on the findings that could be the source of a severe security threat. The detail contained in each finding allows you to dig deeper into the potential issue. This may include Region, resource ID, principal ID, API, the threat list name, or port, for example.
Pricing
A security service that can seemingly detect and analyze huge amounts of data while learning both safe and malicious activity patterns within your infrastructure… You’re probably thinking, how much is this going to cost me?
Thankfully, AWS has provided a free trial for the service upon first activation. You’ll have 30 days and full access to the service to see if it’s a good fit for your security strategy and processes. To estimate the costs going forward, Amazon GuardDuty will generate an estimate of how much you would have spent outside your free trial.
Amazon GuardDuty pricing is based on the quantity of analysis of your AWS log data. Your VPC Flow Logs and DNS Logs will be charged per GB, per month of analysis. Your CloudTrail Event Logs are charged per 1,000,000 events, per month. For monthly information on specific charges per region, see the AWS Pricing page.
Bottom line: Amazon GuardDuty uses machine learning to optimize and analyze potential security threats within your AWS environment without impacting the performance of ANY of your existing services and workloads. In essence, this looks to be a great addition to the security and compliance service category.
I’ll be at re:Invent all week, attending sessions and working at the Venetian Expo Hall, booth 1702. Come by and say hello, or follow me on Twitter @Stuart_A_Scott for further updates.



